I’ve been using a F5 BIG IP in a test lab as a VPN concentrator using client certs as part of the Authentication of the client. We have a windows 2008 r2 domain controller on the inside LAN running MS Certificate Services. The 2008r2 host is running as the Certificate Authority (CA) and is used to issue the client certs that are used in the Auth process.
The key here is that the BIG IP must have access to the Certificate Revocation List (CRL) from that 2008 r2 CA. So I started looking into Online Certificate Status Protocol (OCSP) and with a little research was able to find the bits needed to get the 2008 r2 server to operate as a OCSP Responder so that the BIG IP could query and list revoked client certs thus preventing those bad certs from being used by clients to establish a VPN Session.
The steps here are to:
1) Setup the MS Certificate Services with an OCSP Certificate Template.
2) Allow the CA to support OCSP responder services.
3) Setup an OCSP Responder
4) Create a Revocation Configuration
So, I started with a working 2008 r2 host.
Setup the MS Certificate Services with an OCSP Certificate Template.
1) Open the Certificate Templates snap-in.
2) Right-click the OCSP Response Signing template, and then click Properties.
3) Click the Security tab. Under Group or user name, click Add.
4) Click Object Types, select the Computers check box, and then click OK.
5) Type the name of or browse to select the computer hosting the Online Responder or OCSP responder services, and click OK.
6) In the Group or user names dialog box, click the computer name, and in the Permissions dialog box, select the Read and Enroll check boxes. Then click OK.
Allow the CA to support OSCP responder services.
Note that the Online Responder must be running 2008 R2 Enterprise or 2008 R2 Datacenter
1) Open the Certification Authority snap-in.
2) In the console tree, click the name of the CA.
3) On the Action menu, click Properties.
4) Click the Extensions tab.
5) In the Select extension list, click Authority Information Access (AIA), and then click Add.
6) Specify the locations from which users can obtain certificate revocation data, such as http://computername/ocsp.
7) Select the Include in the online certificate status protocol (OCSP) extension check box.
8) In the console tree of the Certification Authority snap-in, right-click Certificate Templates, and then click New Certificate Templates to Issue.
9) In Enable Certificate Templates, select the OCSP Response Signing template and any other certificate templates that you configured previously, and then click OK.
10) Double-click Certificate Templates, and verify that the modified certificate templates appear in the list.
Setup an OCSP Responder
An OCSP responder is basically a 2008 r2 Enterprise or Datacenter server Running the Online Responder role service in the Active Directory Certificate Services.
1) Open the Certification Authority snap-in.
2) In the console tree, click the name of the CA.
3) On the Action menu, click Properties.
4) Click the Extensions tab.
5) In the Select extension list, click Authority Information Access (AIA), and then click Add.
6) Specify the locations from which users can obtain certificate revocation data, such as http://computername/ocsp.
7) Select the Include in the online certificate status protocol (OCSP) extension check box.
8) In the console tree of the Certification Authority snap-in, right-click Certificate Templates, and then click New Certificate Templates to Issue.
9) In Enable Certificate Templates, select the OCSP Response Signing template and any other certificate templates that you configured previously, and then click OK.
10) Double-click Certificate Templates, and verify that the modified certificate templates appear in the list.
And Finally, Create a Revocation Configuration
Microsoft has this information available here.
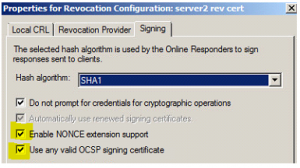
If you plan on using this Online Responder to answer requests from non-MS sources, you may need to set a few additional options for NONCE support and ‘allow all valid requests’.
1) Open Server manager
2) Navigate to Roles -> Active Directory Certificate Services -> Online Responder
3) Highlight Revocation Configuration
4) Right click on the Revocation Entry From the center column and select ‘Edit Properties’
5) In the Properties Window, click the Signing Tab
6) Here you can enable NONCE Support if needed.
7) ‘Use any valid OCSP signing